
A critical vulnerability has been identified in the Next.js React framework, posing a significant security risk by allowing attackers to bypass middleware-based authorization checks under specific circumstances.
The flaw, identified as CVE-2025-29927, has received a CVSS severity rating of 9.1 out of 10, underscoring its critical nature.
According to Next.js, the vulnerability revolves around the improper handling of an internal header called x-middleware-subrequest, which is normally employed to avoid recursive request loops.
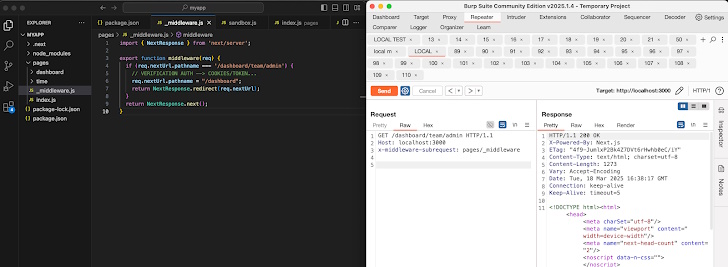
"It was possible to bypass middleware execution, enabling malicious requests to evade critical security validations, such as checks for authorization cookies, and directly access protected routes," Next.js stated in their advisory.
The vulnerability has been patched in Next.js versions 12.3.5, 13.5.9, 14.2.25, and 15.2.3. Users who cannot immediately apply these patches are strongly advised to block external requests that include the x-middleware-subrequest header from reaching their applications.
Security researcher Rachid Allam (known as zhero and cold-try), who discovered and responsibly disclosed the vulnerability, has published additional technical details, highlighting the urgency for users to update promptly to mitigate exploitation risks.

Add new comment