
In 2025, the cyber security landscape was shaken by the official debut of the Belsen Group – a new group that exploited over 15,000 vulnerable configurations of FortiNet firewalls in 144 countries. This event not only highlights the risks associated with known vulnerabilities but also serves as a lesson about the importance of compromise assessments and prompt remediation.
The Belsen Group entered the cyber scene with a post on the dark web stating:
At the beginning of the year, and as a positive start for us, and in order to solidify the name of our group in your memory, we are proud to announce our first official operation.
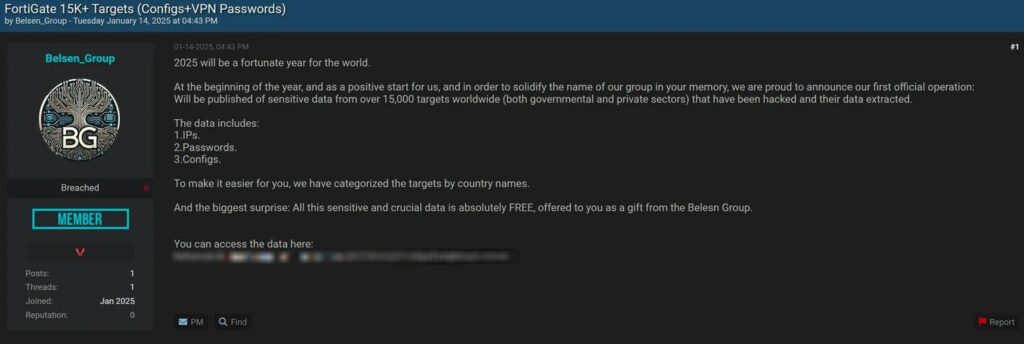
This statement suggests that the group aims to quickly establish itself in the cyber threat landscape. The page on Malpedia provides details about the group’s tactics and profile, emphasizing their emerging character and intent to create a lasting impact in the collective memory of cyber security professionals.
The vulnerability CVE-2022-40684, identified nearly three years ago, allows unauthenticated attackers to exploit the administrative interface of FortiNet devices using specially crafted HTTP/HTTPS requests. Affected versions include:
- FortiOS: 7.0.0 – 7.0.6 and 7.2.0 – 7.2.1
- FortiProxy: 7.0.0 – 7.0.6 and 7.2.0
- FortiSwitchManager: 7.0.0 and 7.2.0
An article from SocRadar explains in detail the exploitation method, showing how attackers managed to identify and exploit the weaknesses of these systems, demonstrating that no old vulnerability should be overlooked.
According to disclosures from the Belsen Group, the attack led to the exfiltration of highly sensitive information, such as IP addresses, detailed device configurations, VPN credentials, and passwords.
This digital "offer," publicly distributed as a sort of "gift" for the beginning of 2025, underscores the severity of the incident. Additionally, the GitHub repository provides technical documentation and concrete examples of the compromised data, aiding in the detailed understanding of the exploitation mechanisms and the structure of the extracted data.
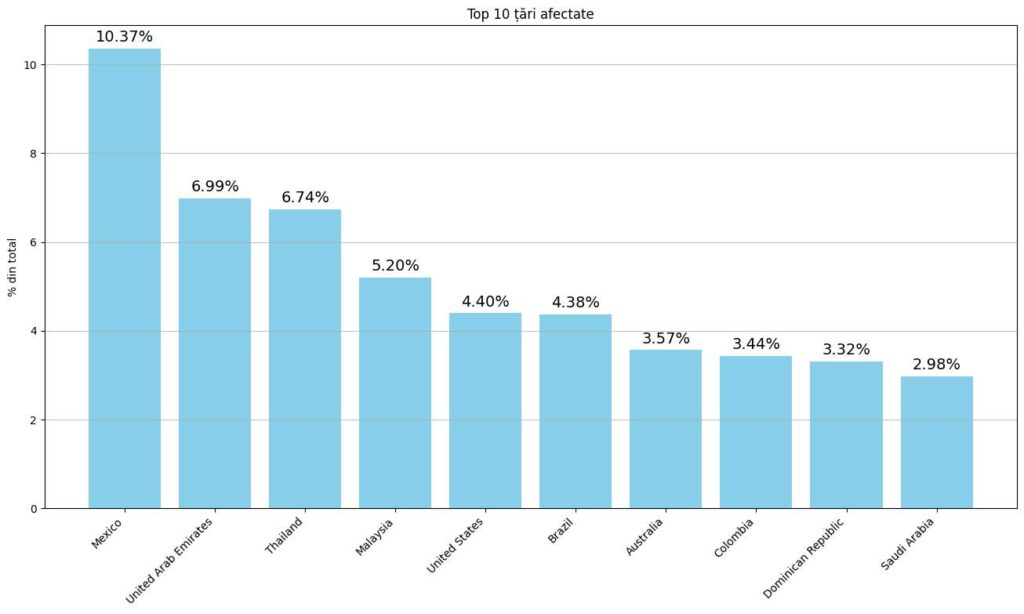
The operation had a global scope, affecting 144 countries, with the following significant distributions:
- Mexico: 1,604 devices (~10.37%)
- United Arab Emirates: 1,081 devices (~6.99%)
- Thailand: 1,043 devices (~6.74%)
- Malaysia: 805 devices (~5.20%)
- United States: 681 devices (~4.40%)
- Brazil: 677 devices (~4.38%)
- Australia: 553 devices (~3.57%)
- Colombia: 532 devices (~3.44%)
- Dominican Republic: 513 devices (~3.32%)
- Saudi Arabia: 461 devices (~2.98%)
In Romania, the 22 compromised infrastructures (approximately 0.14% of the total) underscore that no system is completely immune, regardless of size or location. Following internal analysis, including recommendations made by specialists in articles from CSO Online and by the manufacturer Fortinet, here are essential measures for protection:
- Change credentials: Immediately after identifying a breach, update all passwords and accesses.
- Apply security patches: Ensure that devices are running the latest versions that fix vulnerabilities.
- Continuous network monitoring: Implement IDS/IPS systems for real-time detection of suspicious activities.
- Review configurations: Reduce privileges, block unused ports, use whitelisting, and disable non-essential services.
- Additional layers of security: Segmenting the network, training staff, and implementing multi-factor authentication (MFA/2FA) can significantly enhance protection levels.
- Incident response plan: Develop and periodically test a response plan to mitigate the impact of a potential attack.
The Belsen Group attack, by exploiting the vulnerability CVE-2022-40684, serves as a harsh reminder that no breach is too old to be considered harmless. System administrators must ensure that security updates/patches are applied promptly, monitoring is conducted continuously, and security measures are regularly reviewed. If you do not want to become a hacker's "favorite gift," it is time to take serious action!

Add new comment